The report deconstructs the tactics, techniques and procedures (TTPs) used in the attack.
SophosLabs believes the attack was the work of a nation state motivated by espionage.
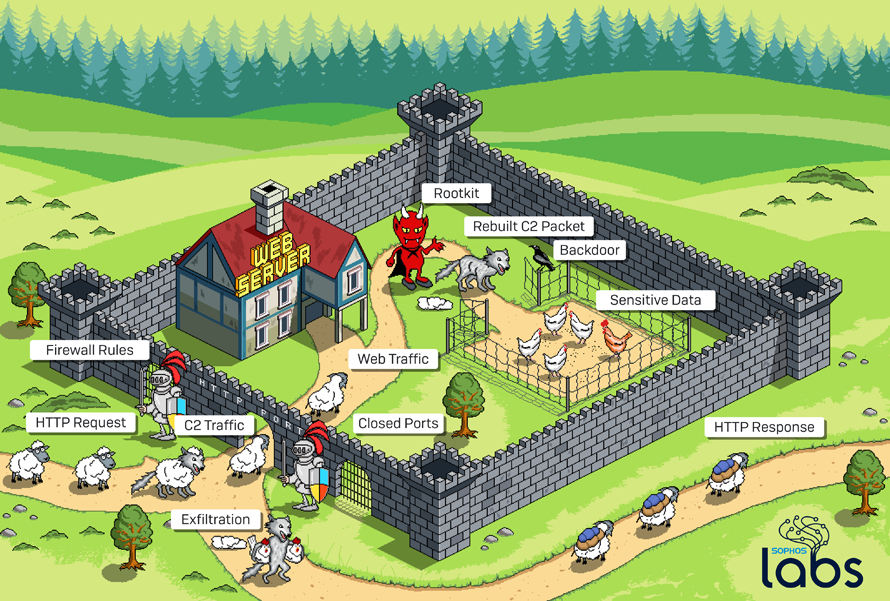
As detailed in the report, the TTPs used together include: a rootkit circumventing firewalls, a rare technique to gain access to servers disguised as normal traffic, and a backdoor payload that shares malicious code between both Windows and Linux operating systems, a known, but uncommon approach.
While each individual element has been observed previously in attacks by highly-skilled adversaries, they have not been seen before in combination.
Sophos expects that this package of TTPs will trickle down to the lower rungs of the cybercriminal hierarchy and be used as blueprints for new firewall attacks.
“This is the first time we have seen an attack formula that combines a bypassing technique with a multi-platform payload targeting both Windows and Linux systems.
IT security teams and network administrators need to be diligent about patching all external-facing services to prevent attackers from evading cloud and firewall security policies,” said Sergei Shevchenko, threat research manager, SophosLabs.
“IT security teams also need to protect against multi-platform attacks.
Until now, Windows-based assets have been the typical target, but attackers are more frequently considering Linux systems because cloud services have become popular hunting grounds.
It’s a matter of time before more cybercriminals adopt these techniques.”
Advice for Defenders
• Create a full inventory of all devices connected to the network, and update all security software used on these devices
• Ensure all external-facing services are fully patched. Cloud hosting services often provide firewall security, but this should not be a substitute for an organization’s own cloud security measures
• Check and double check all cloud configurations. The Sophos 2020 Threat Report reveals that user misconfiguration and lack of visibility are the top causes of attacks in the cloud
• Enable multi-factor authentication on any security dashboards or control panels used internally to prevent attackers from disabling security products during an attack
• Remember, there is no single silver bullet for security, and a layered, defense-in-depth, next generation security model – including components designed specifically to protect data and networks in the cloud, like Sophos Cloud Optix with Sophos Intercept X for Server – is an essential best practice
For additional information, please reference this SophosLabs Uncut article.