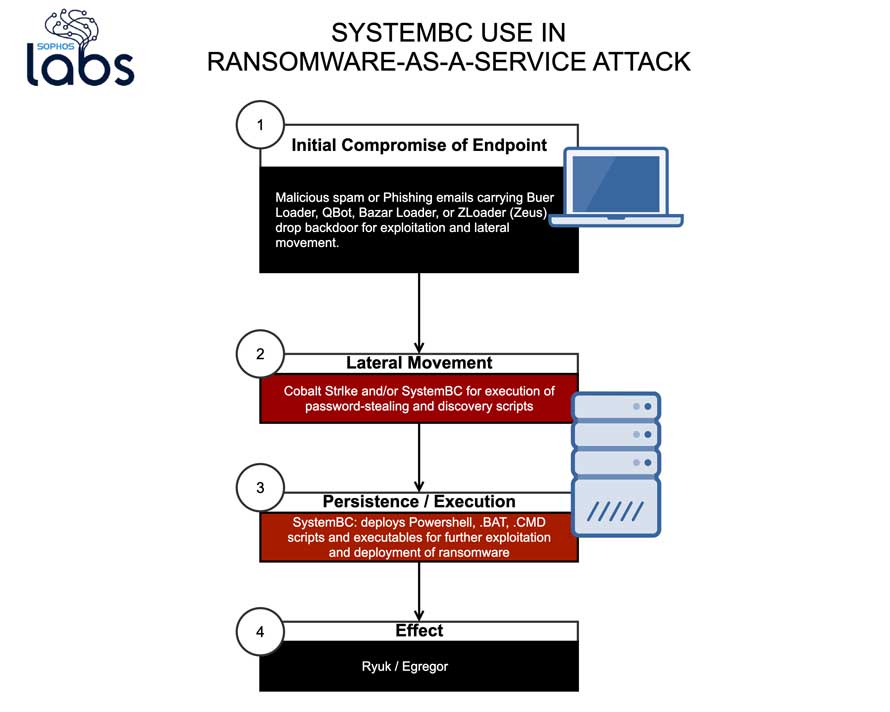
The research shows how SystemBC has developed into a fully-fledged remote access tool that acts as a Tor proxy and is being used in ransomware-as-a-service attacks for communications, data exfiltration and the download and execution of malicious modules.
SystemBC was first discovered in 2019, operating like a “virtual private network” via a SOCKS5 proxy.
A year on, the upgraded version analysed by Sophos provides attackers with a persistent backdoor that automates a number of key activities so that operators can launch multiple attacks without the need for hands-on-keyboard activity.
It can execute Windows commands passed over the Tor connection, as well as deliver and execute scripts, malicious executables and dynamic link libraries (DLLs).
Sophos’ research is based on investigations into recent ransomware-as-a-service attacks involving Ryuk and Egregor, which all deployed SystemBC.
The investigations show that SystemBC is used in combination with different commodity tools, creating a diverse profile of tactics, techniques and procedures (TTPs).
For instance, in some of the Ryuk attacks investigated SystemBC was deployed alongside Buer Loader malware, while other attacks in the same campaign used Bazar or Zloader.
The Egregor attacks that Sophos investigated used SystemBC together with Qbot.
“We are increasingly seeing ransomware operators outsource the deployment of ransomware to affiliates using commodity malware and attack tools,” said Sean Gallagher, senior security researchers, Sophos.
“SystemBC is a regular part of recent ransomware attackers’ toolkits— Sophos has detected hundreds of attempted SystemBC deployments worldwide over the last few months.
The backdoor can be used in combination with other scripts and malware to perform discovery, exfiltration and lateral movement in an automated way across multiple targets.
These SystemBC capabilities were originally intended for widespread commodity malware, but they have now been folded into the toolkit for targeted attacks—including ransomware.
“The use of multiple tools in ransomware-as-a-service attacks creates an ever more diverse attack profile that is harder for IT security teams to predict and deal with. Defense-in-depth, employee education and human-based threat hunting are essential to detecting and blocking such attacks.”
A list of IOCs for SystemBC is posted on SophosLabs’ GitHub page.
Further information on System BC and other cyberthreats can be found on SophosLabs Uncut where Sophos researchers regularly publish their latest research and breakthrough findings, such as Egregor Ransomware: Maze’s Heir Apparant and Inside a New Ryuk Ransomware Attack.
Threat researchers can follow SophosLabs Uncut in real time on Twitter at @SophosLabs.